What it takes to get developers engaged with security

Post 1 in a series our autumn 2022 on Application Security.
Okay, so we all know developers are great problem solvers. Every day they harness this superpower of turning ideas into reality. However, with great power comes even greater responsibility. That means ensuring they create secure applications can be more important than making sure they deliver that exciting new feature on time.
Something’s got to change — the state of application security today
Interestingly, a recent report from Salt Security (2022) suggests that 62% of its respondents had slowed the rollout of code to production because of security concerns. Not getting that valuable new product feature out on time can hurt your bottom line but detecting security vulnerabilities earlier in the development cycle can be nearly 100 times cheaper per bug than fixing them once discovered in a production system. (IBM X-Force)
So what can we do about this increasingly complex conundrum? You may think you already know the answer, “it’s so simple, let the security team take care of it!”. We hear you, except your security team is more than likely already struggling to designate the appropriate amount of time to address your security concerns. Besides, security should be the responsibility of every employee.
Maybe you’re willing to admit that something’s got to change, perhaps you’re all in on secure code training and upskilling for your developers. Immersive Labs has already got you covered for a wide array of secure coding topics and languages that ensure your team of developers can stay informed, identify poor practices, and genuinely understand the implications of not writing secure code with real-world examples that emphasize the tangible cost of introducing or ignoring vulnerable code. We do all of this using real development environments and technologies to remove the disconnect between what is learned and how to apply this newfound knowledge in a devs day to day workflow.
Except, the day-to-day workflow for most developers doesn’t include dedicated time for upskilling in security aspects of coding. In fact, “Only 27% of front-line developers view the security of applications as a critical part of their responsibilities”. (Osterman Research (2021)). It’s time to get them more engaged.
The old proverb, “You can lead a horse to water but you can’t make it drink.”, sums up this dilemma rather well.
Secure coding competition collection
Here at Immersive Labs, the application security team has been busy creating our secure coding CTF to tackle that issue head-on. A series of labs designed to challenge juniors all the way through to lead developers over five languages: Python, Java, C#, Go, and Node.js.
This collection of labs is run as an event over a timespan that suits your team’s needs. We give your devs engaging environments mixed in with a healthy dose of competition for the perfect concoction of challenging content, fun, and bragging rights.
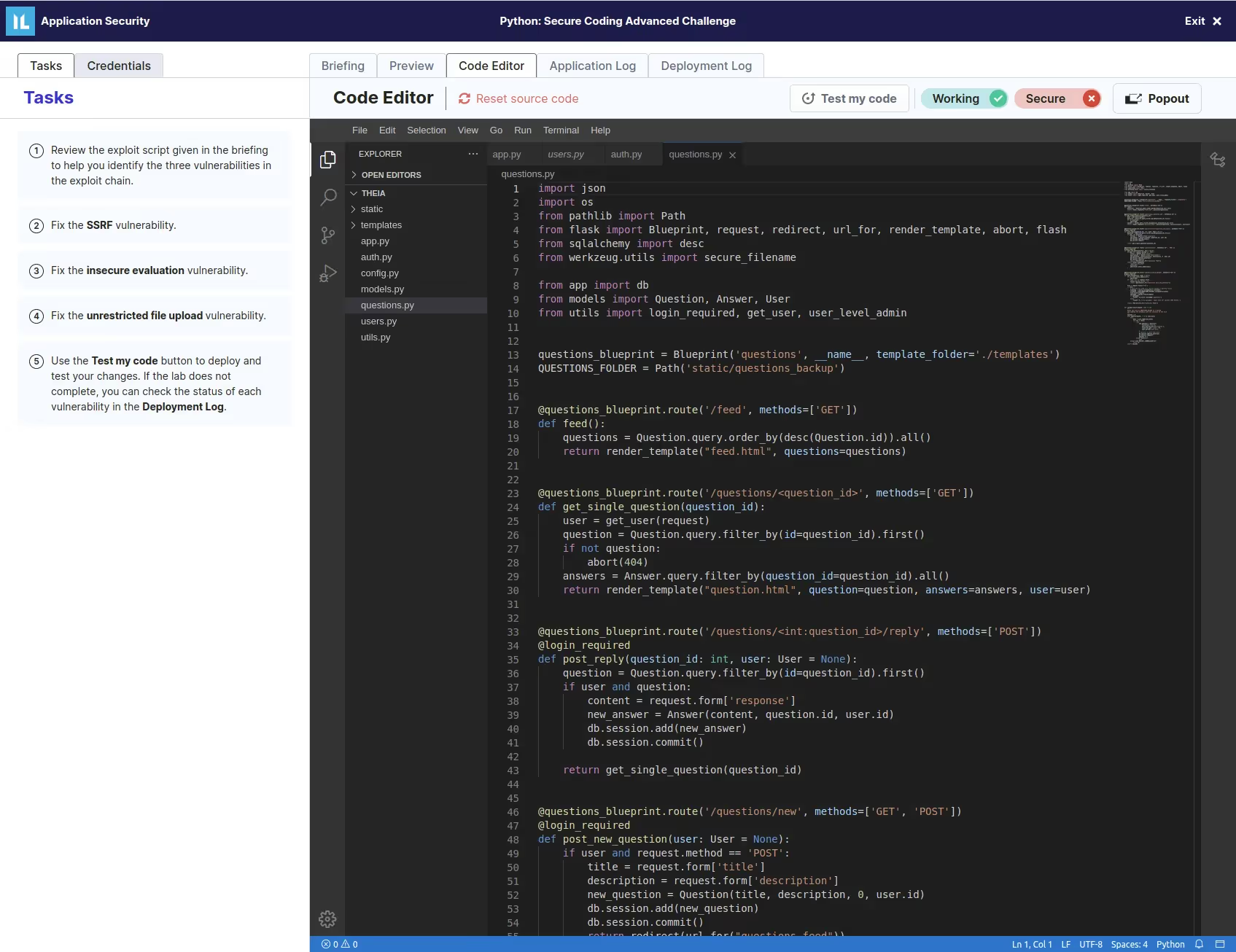
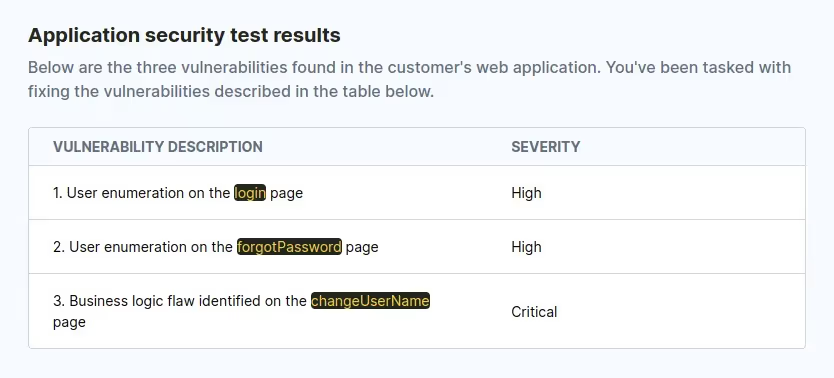
As they navigate through these increasingly difficult labs they’ll be tasked with finding and fixing vulnerabilities from a pentest report.
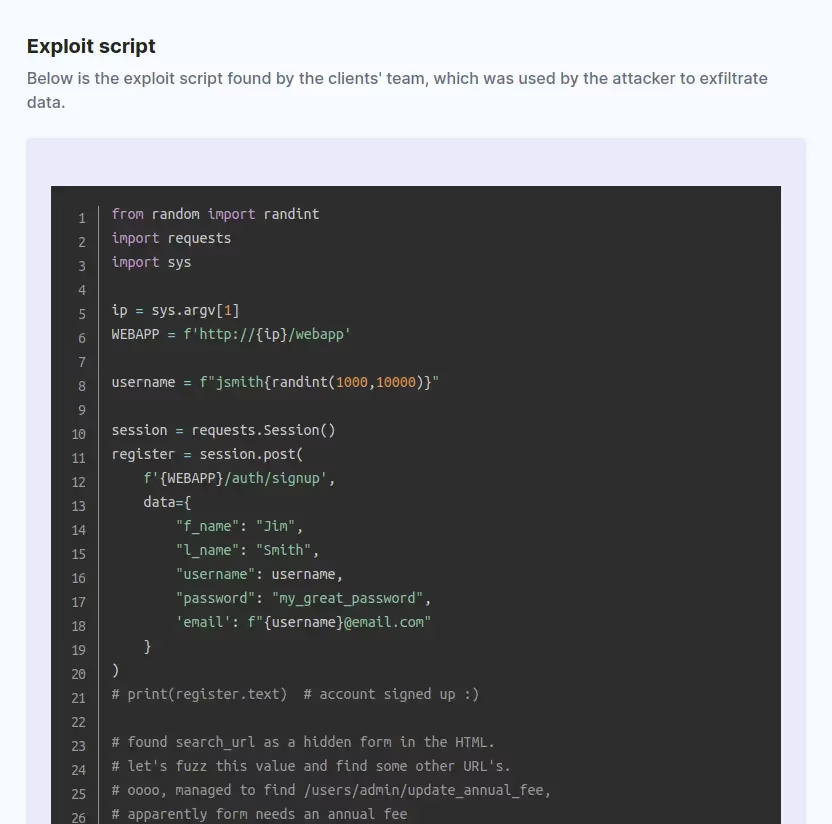
If you have what it takes to make it all the way to one of our advanced challenges you’ll be faced with the opportunity to reverse engineer a hacker’s exploit script (aka Proof of Concept [PoC]) to discover how the application was breached and to fix the vulnerabilities that they used!
Completing them all will earn them a spot at the top of the leaderboard and the moniker as an application security go-to within their team.
This level of immersion eradicates the lack of purpose felt in typical classroom learning and most importantly exposes your developers to learning opportunities that can be reinforced through our extensive catalog of secure-coding labs aimed at upskilling through a wide range of secure-coding practices.
If you’re already a customer of Immersive Labs, contact your Customer Success Manager for access.
If you’d like to learn more about the current maturity of application security practices amongst developers, please download our research report, “Imperfect people, vulnerable applications” – our study with Osterman Research explores the human elements that influence cyber risk in the Software Development Lifecycle.





.svg)






.svg)






.svg)

Ready to Get Started?
Get a Live Demo.
Simply complete the form to schedule time with an expert that works best for your calendar.





.svg)
.webp)





