Netgear vulnerabilities could put small business routers at risk
Netgear has released a set of updated firmware for multiple devices to resolve a number of security vulnerabilities responsibly disclosed by researchers at Immersive Labs. These could lead to unauthorized access to devices or modification of the internal filesystem that can be abused to affect traffic passing through the device.
Findings
PSV-2021-0169 & PSV-2021-0172: Post-Authentication Command Injection
CVSS Rating: High
CVSS Score: 7.8
With authenticated access to affected Netgear devices, it is possible to modify settings in the administration panel to run arbitrary commands on the router. This kind of command injection also adds persistence which means even if the router is restarted or updated, the vulnerability can persist.
Traditional command injection vulnerabilities target the commands that are being executed by the webserver component. The common example of this is routers that let you run the ping command if user input is not properly sanitized, after which attackers can then run arbitrary commands.
In these two vulnerabilities, we only use the web server to change the configuration values that are then saved to the device. Once these entries are saved, every time the device starts a set of bash scripts or other custom executable files on the device read these variables from the configuration and use them to execute commands. These scripts and binaries do not apply the same filters that are traditionally found when the web application is parsing untrusted input.
These commands could be used to open additional ports or to allow command-line access over the network to the operating system. With operating system access, a determined user with malicious intent could have a significant impact on the availability of the device and the data that is passed through it.
PSV-2021-0171: Sensitive Information Disclosure
CVSS Rating: Medium
CVSS Score: 6.2
With this vulnerability, an attacker with access to the local network can make a request to the router’s UPNP port and view the device serial number. Whilst this may sound fairly innocuous this serial number is used as part of the password reset function on most Netgear devices.
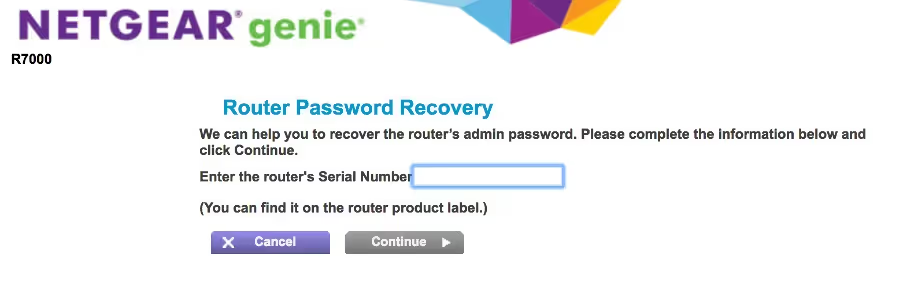
This mechanism is supposed to ensure only those with physical access to the device can reset the password. Armed with this information it is now possible for any user on the network to brute force the password reset questions or, potentially, combine this with a side-channel attack like the one disclosed earlier this year by Microsoft.
Whilst we recognise that the CVSS scores may come in High for the command injection vulnerabilities, the likelihood of an attacker exploiting these vulnerabilities in a live network remains low. There is still a valid threat surface and whilst it remains in the realms of “Hackers Could“ it is always important when considering security vulnerabilities to look past the traditional exploit methods and put yourself in the shoes of an attacker. How could they abuse this?
Hackers Could infect SOHO routing devices and resell them.
Using the vulnerabilities outlined above it is possible to add new files and configurations to one of these devices that could survive a reset of the device. It would also be possible to block any future firmware updates keeping the compromised device in this state. Listing this device on eBay or other tech reseller websites and repackaging the device in the box so it appears brand new could put users at risk. With more home users relying on their home IT, this kind of attack could result in access to corporate data. I will finish this by saying, “Hackers could, they probably won't”
Timeline
- May: 3 vulnerabilities disclosed via BugCrowd platform
- June: 3 additional findings discovered.
- 25th June: Immersive Labs asked Netgear if we could publicly disclose findings after patches are released, and if we could include the 3 already reported via bugcrowd
- 2nd July: Netgear asked Kev Breen from Immersive Labs to send all the findings directly and asked for a 120 day disclosure period
- 5th July: Kev Breensent copies of all reports including bugcrowd submitted reports accepting 120 days
- 13th July: Immersive Labs submitted an additional Command Injection finding
- 14th October: Netgear asked for more details and an extension to the disclosure period
- 15th October - Immersive Labs agreed to the extension
- 30th November - patches released by Netgear

Kev Breen,
Director of Cyber Threat Research,
Immersive Labs
@kevthehermit





.svg)






.svg)






.svg)

Ready to Get Started?
Get a Live Demo.
Simply complete the form to schedule time with an expert that works best for your calendar.





.svg)






