Prove Your Microsoft Sentinel Detection Logic Against Real-World Threats, Now on Immersive One
Prove Your Microsoft Sentinel Detection Logic Against Real-World Threats, Now on Immersive One
Effective incident response combines muscle memory and tool proficiency. Yet, for teams relying on Microsoft Sentinel, a persistent gap exists between training exercises and production reality. Practicing on theoretical data or unfamiliar, locally-installed SIEMs doesn't prepare a SOC Lead for a live breach in their own cloud environment.
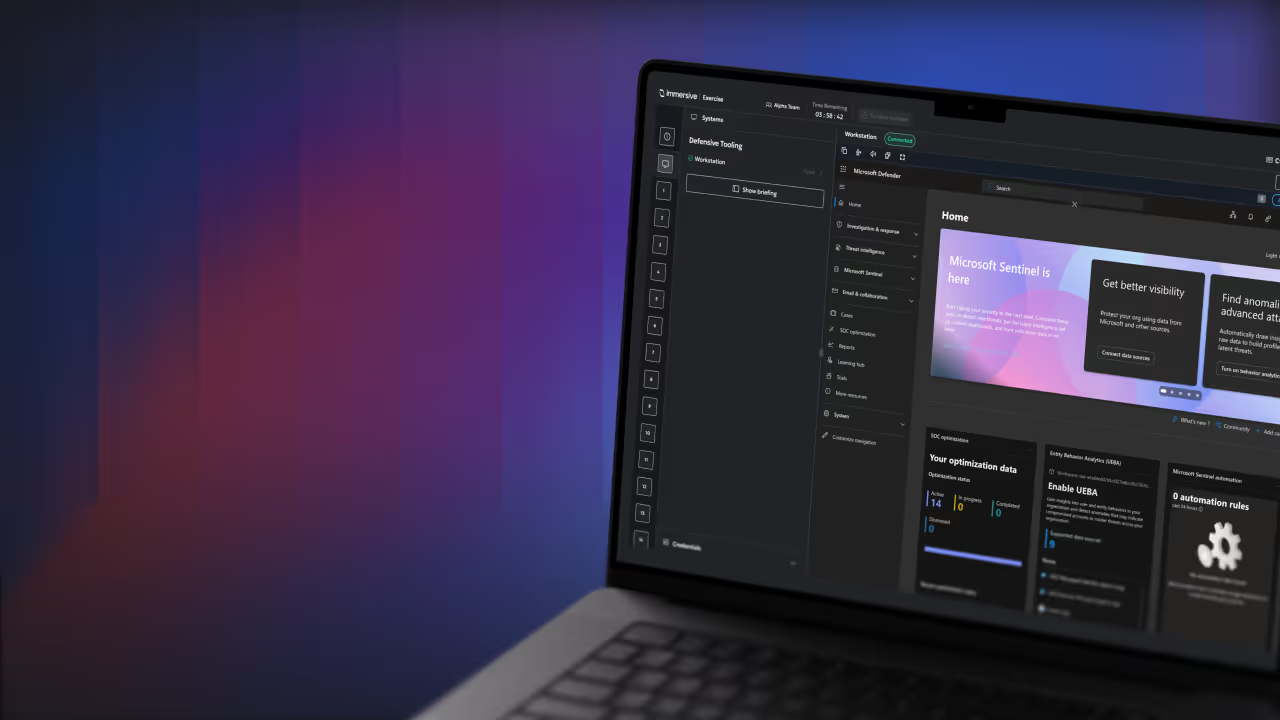
Immersive One enables teams to close that gap with a dedicated Microsoft Sentinel SIEM module, marking the next milestone in the Dynamic Threat Range roadmap. Teams can now ingest live simulation telemetry into a dedicated Sentinel instance to practice, hunt, and validate detections within their actual production workflows.
Bringing your people, processes, and tools into a single operating loop removes the guesswork from proving, improving, and benchmarking readiness. Here’s what that looks like in practice.
Bringing Microsoft Sentinel to Dynamic Threat Range
With Immersive One’s Dynamic Threat Range capability, organizations already glean deep investigative value through its established Splunk and Elastic environments. Now, with native support for Microsoft Sentinel, they can standardize and validate cloud-native security operations within the ecosystem they rely on every day.
Through secure API integration, simulated attack telemetry is streamed directly into a dedicated Sentinel instance. This removes the barrier between training and production. The result is a true-to-life environment where teams can prove readiness using the same tools, logic, and workflows they depend on in real-world scenarios.
Gain Confidence Mastering the Mission in Production Workflows
Even highly skilled SOC analysts can lose critical time under pressure when navigating unfamiliar interfaces. By operating directly within Microsoft Sentinel, teams eliminate that friction. They can run live KQL queries, build workbooks, and investigate simulated attacks in the environment they rely on. This approach builds practical, tool-specific muscle memory to reduce response times and improve decision-making when it matters most.
Validate Detection Rules and Playbooks
A SIEM is only as effective as the logic behind it. With access to live, simulated attack telemetry, you can test custom Microsoft Sentinel detection rules and response workflows in a controlled, high-fidelity environment. This ensures a proactive approach that validates your team’s proficiency. You gain the empirical data required to:
- Harden your detection queries against realistic noise to eliminate false positives.
- Ensure your automated and manual response workflows trigger exactly as designed.
- Demonstrate that your specific configurations function against modern threat vectors before they ever touch your production tenant.
Ultimately, you can be confident that your configurations will perform against modern threat vectors, not just in theory, but in practice.
Measure Performance and Benchmark Readiness
Operating within a cloud-native SIEM allows you to capture accurate Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) within a high-fidelity environment. By removing tooling friction and exercising within familiar workflows, teams can focus on what matters most: investigation, analysis, and containment.
Since exercising occurs in a mirrored production environment, performance data reflects true capability; you’ve removed the variables that skew performance data. This provides a reliable foundation for benchmarking resilience against industry peers and meeting the expectations of regulatory frameworks.
Raising the Bar for Resilience in Cloud-Native Enterprises
With Immersive One, readiness moves beyond theory. You can prove resilience with measurable insight into how your teams perform in real-world conditions, where speed, coordination, and decision-making matter most.
The new Microsoft Sentinel integration grounds that proof in your day-to-day operations. Teams operate within familiar SecOps workflows, validating detection and response, refining playbooks, and benchmarking performance in context. You can be confident at the operational level and deliver clear, defensible evidence to stakeholders that your organization is ready to withstand modern, cloud-driven threats.
Since cloud environments continue to evolve, upcoming Azure-specific scenarios and sophisticated hybrid-cloud attack simulations will further extend this capability. Rest assured, with Immersive One, your resilience strategy can keep pace with increasingly complex, cloud-native architectures.
Get Started
- Already using Dynamic Threat Range with Immersive One? Log in to your Immersive One platform to start using the new Microsoft Sentinel SIEM module.
Exploring Immersive for the first time?Book a demo to see how Immersive One enables you to validate your team's performance using your own security stack.

See how to prove readiness with one platform.
See how Immersive One helps technical teams and leaders prove readiness, close capability gaps, benchmark progress, and report cyber resilience with confidence.




















.svg)
