Prove Decision-Making Under Pressure
Strengthen Crisis Response
Assess Response Effectiveness in Real-Time Simulations
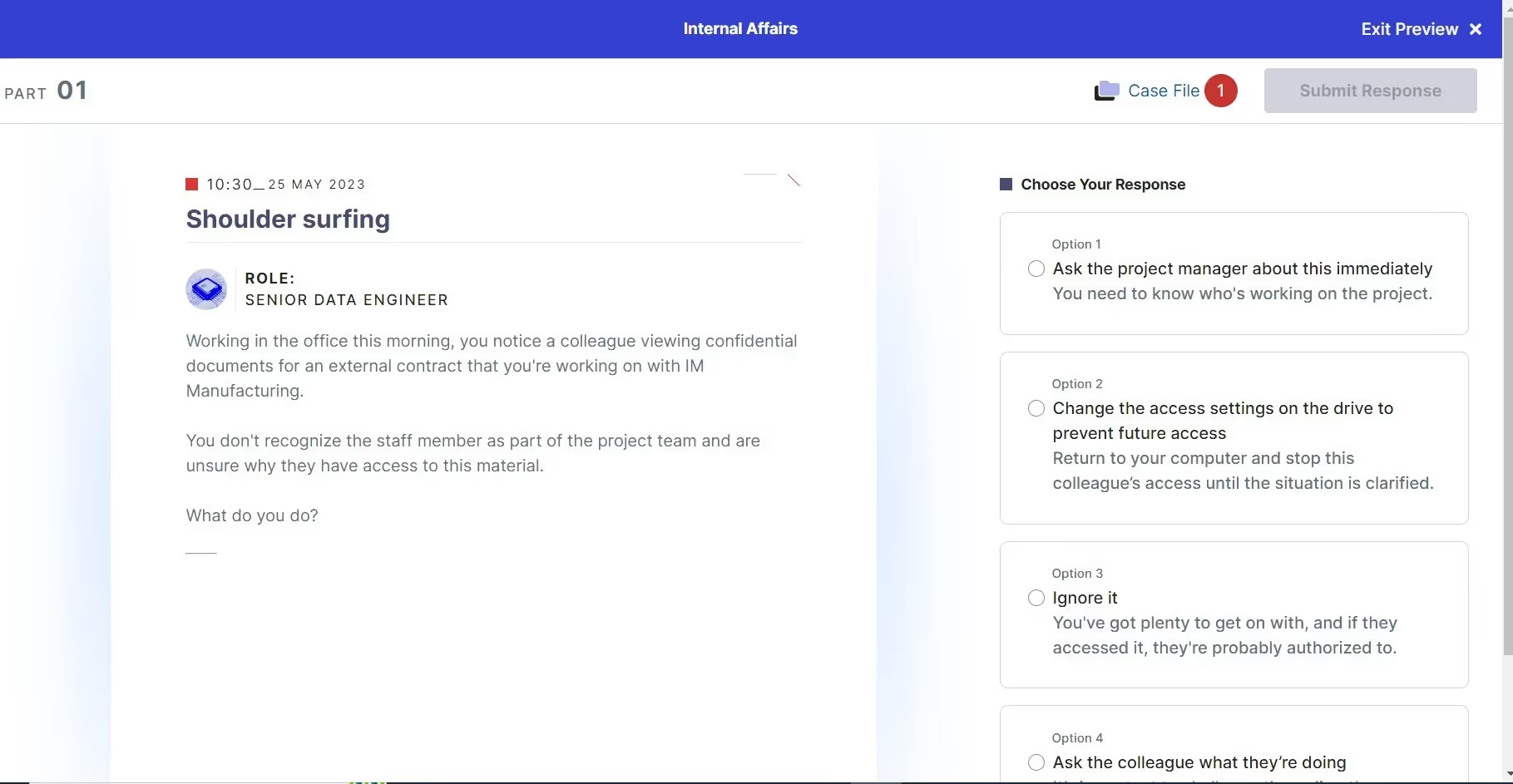
Crisis Sim scenarios emulate authentic cyber threats, challenging teams to prioritize actions, assess risks, and make decisions under tight time constraints – just like in real-world breaches.
Test Leadership and Coordination in Crisis Scenarios
Assess how leadership, technical teams, and key stakeholders collaborate under pressure, ensuring alignment in decision-making and communication during live simulations.
Generate Insights with Comprehensive Metrics
Generate detailed analytics on your team's crisis response capabilities, including decision latency, accuracy, and strategic outcomes, to pinpoint improvement areas across departments.
Prove Resilience Across Crisis Scenarios
Test your organization’s ability to adapt to escalating cyber threats while maintaining operational integrity, ensuring your defenses are robust under the most challenging of conditions.
Prove Leadership and Team Coordination
Optimize Crisis Collaboration
Understand and enhance your organization’s resilience with actionable scoring metrics that quantify readiness and showcase your ability to handle real-world cyber threats.

Real-Time Collaboration Scenarios
Experience scenarios that challenge C-suite leaders, technical teams, and communication specialists to work together seamlessly in high-pressure, real-world crisis situations.

Crisis Leadership Insights
Uncover how leaders delegate, prioritize, and respond under pressure, turning technical input into actionable strategies for effective crisis management.

Role-Specific
Analysis
Gain insights into how individuals and teams contribute during a crisis. Highlight areas for improved collaboration and develop targeted strategies for better team synergy.

Stress Testing for Alignment
Simulate escalating crises to challenge your team's adaptability, communication flow, and decision-making, helping build stronger cross-functional collaboration.
Prove Your Skills
With Real-World Exercises
Immersive Crisis Sim challenges teams with dynamic, real-world scenarios that test decision-making, collaboration, and resilience under pressure.
Dynamic, Real-World Simulations
Real-life crises with dynamic storylines challenge teams using various threat actors and attack vectors.
AI-Powered Scenario Generator
Choose from an extensive catalog or fire up our Scenario Generator to create tailored content in minutes.
Actionable Insights
Analyze the financial, operational, and reputational impacts of your team's decisions to guide improvements.
Prove Operational Impact and Response Effectiveness
Mitigate Crises With Precision
Demonstrate how your organization mitigates real-world crises while minimizing financial, operational, and reputational fallout.
Quantify Impact Across Metrics
Evaluate the immediate effect of your decisions on stability, operational continuity, and reputational standing.
Simulate Crisis Recovery
Assess how effectively teams restore normal operations and adapt processes post-crisis.
Highlight Strategic Gaps
Identify vulnerabilities in decision pathways to strengthen organizational resilience.





.svg)






.webp)



















.svg)