On Monday 10th February 2020, the US charged four Chinese nationals with executing a huge 2017 cyberattack on Equifax. In this blog we take you from the launch of that attack right up to the recent indictment of its alleged perpetrators. We have also included links to some relevant labs on our platform – many of which you can try for free on Immersive Labs Lite.
When did this all start?
Around May 13th–July 30th 2017.
What happened?
Attackers launched a cyberattack against consumer credit rating agency Equifax, which stores a huge amount of personal information. The US Department of Justice alleges that members of the People’s Liberation Army (the armed forces of the People’s Republic of China) are to blame.
The attackers stole data including names, birthdates, addresses, social security numbers, drivers’ license numbers and credit card numbers relating to 147 million-plus Americans – roughly 40% of the population. Around 1 million UK and Canadian customers were affected too. The attackers were also accused of stealing trade secrets such as data compilation and database designs.
Equifax did not make the breach public until September 2017, despite discovering it at the end of July.
How was the attack executed?
On March 7th 2017 Apache announced a vulnerability in the Apache Struts 2 web framework (CVE-2017-5638), which Equifax used for its online dispute portal. This vulnerability enabled outside parties to trick Struts into executing malicious code, and had the potential to leave any systems running on Struts open to further attack. Although Apache released a patch for this issue on March 9th 2017, Equifax failed to install it.
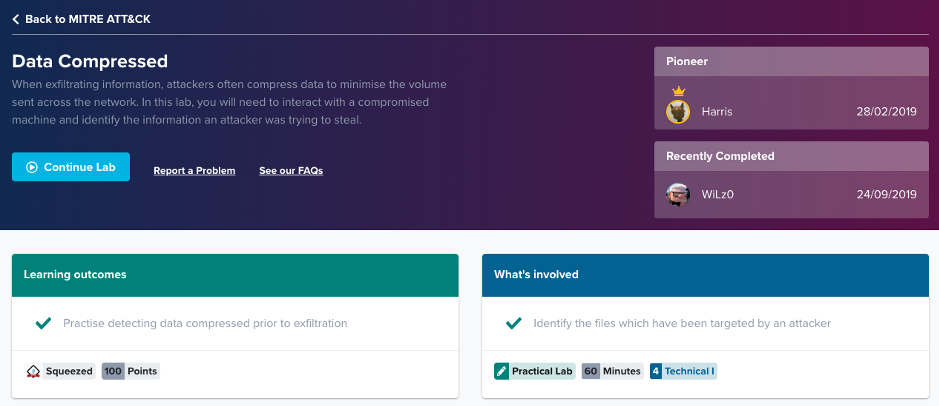
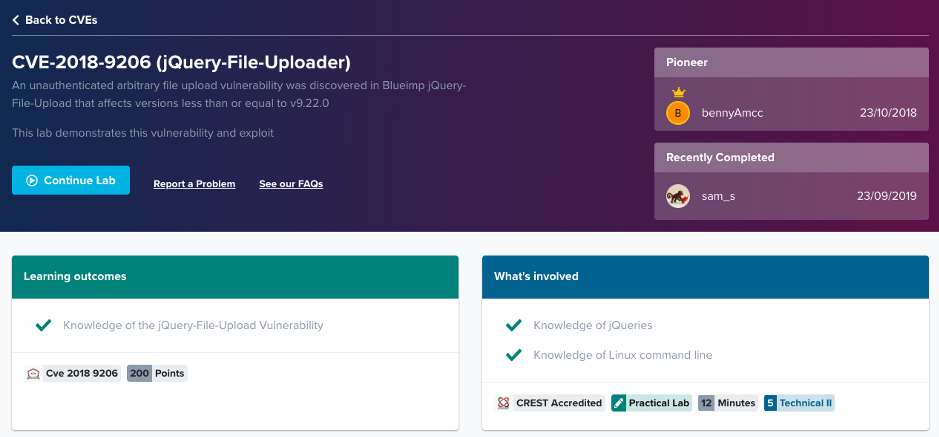
The attackers used this vulnerability to upload unauthorized web shells to an Equifax web server. Subsequently, they were able to access back-end databases and search for PII, as Equifax had not ensured that its systems were adequately segmented. Equifax also had usernames and passwords stored in plaintext within its system, and had failed to renew an encryption certificate on an internal security tool. Equifax used this tool to monitor outbound encrypted traffic; because its certificate was not renewed in a timely manner, it did not function properly for around 10 months. The attackers were able to exploit this; they encrypted the data that they’d moved through the Equifax system, and Equifax remained unaware that they were failing to monitor this. It was only in July of 2017, when the certificate for this tool was finally reviewed, that the attack was uncovered.
Logs show that the attackers ran around 9,000 SQL queries during the course of the incident.

This lab is only available on the full Immersive Labs platform. If you want to get a taster of our labs for free, head over to Immersive Labs Lite where you’ll find some of the labs mentioned in this blog!
Detailed timeline
May 13th 2017– Apache Struts vulnerability exploited. A web shell was created to grant backdoor access to the ports and allow conspirators to obtain database service login credentials. The attackers undertook reconnaissance, running a series of queries to identify the database structure of Equifax and number of records within. The attackers used Apache Struts commands, malicious web shells created through Apache Struts, and SQL commands.
Sometime between May 14th–July 24th – A file containing PII was accessed, stored in output files and split into smaller segments for download.
June 16th – A China-based IP address logged into a Taiwanese IP address via Remote Desktop Protocol. Malicious file jndi.txt was copied and an identical webshell was uploaded into the Equifax network.
July 5th – A Swiss IP address accessed the Equifax network and queried a database for social security numbers.
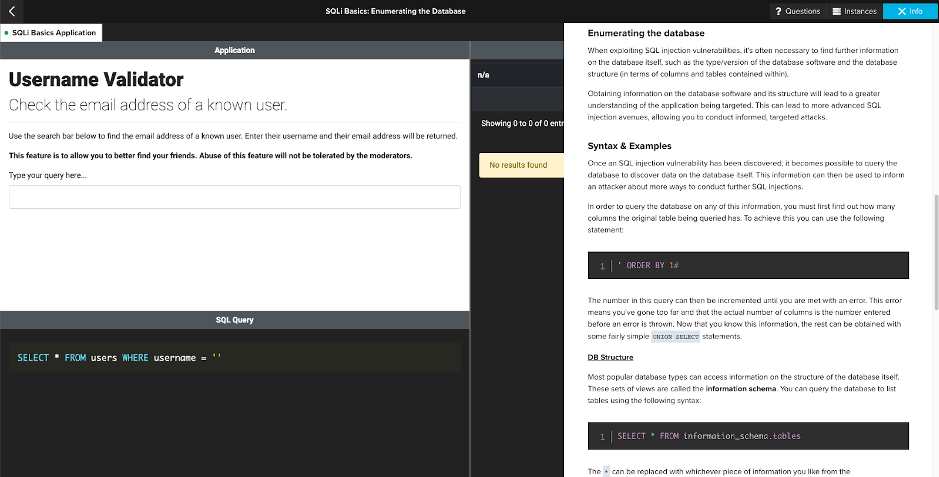
Red and Blue Team Lab: SQLi Basics: Enumerating the Database
July 6th – The Swiss server accessed Equifax again, querying a database for names, addresses and social security numbers. The results were put into an output file, and a compressed file archive was created before being copied into a different directory. After being downloaded, this archive was deleted. On the same day, another back-end database was accessed through the Swiss server.
July 7th – A third back-end database was accessed and queried via the Swiss server. A second China-based server was used to exploit the Apache Struts vulnerability on Equifax’s online dispute portal. On this day and July 9th, a third Chinese server was used to conduct reconnaissance on Equifax’s online dispute portal.
July 10th – A fourth China-based IP address logged into the Taiwan server and copied malicious file abc.txt there. A fifth China-based IP address used a malicious web shell previously installed on Equifax’s system to download abc.txt from the Taiwan server. China server five was then used to upload a substantively identical web shell to Equifax’s network.
Mid July – The Swiss server was used to connect to Equifax’s network and create an archive containing 49 directories. This was split into 600-megabyte segments and downloaded from the Equifax network to a Dutch server via HTTP commands.
Mid July – A sixth Chinese server used a malicious web shell to query an Equifax data table and store results in output files. Using the same Chinese server, this was then compressed to an archive file and downloaded. A web shell was then used to delete the archive from Equifax’s network to obscure the theft.
Late July – The second Chinese server was used to access a malicious web shell on the Equifax server to allow an attacker (named in the indictment as Wang) to issue unauthorized SQL commands on an Equifax back-end database.
Late July – A Singapore-based IP address used the same malicious web shell to run additional queries.
Late July – The Singaporean server was used to access the malicious web shell on Equifax’s server.
Up until July 30th – PII repeatedly stolen from the Equifax back-end databases.
Why?
In a press conference Attorney General William Barr explained why the Chinese government might target Equifax: “For years we have witnessed China’s voracious appetite for the personal data of Americans. This data has economic value, and these thefts can feed China’s development of artificial intelligence tools as well as the creation of intelligence targeting packages.”
The Equifax prosecution is evidence of ongoing tension in the cyber space between America and China, and America’s increasingly aggressive stance on Chinese espionage operations targeting its citizens.
Indictment
On Monday 10th February 2020, the US charged four Chinese nationals – Wu Zhiyong, Wang Qian, Xu Ke and Liu Lei – with carrying out the attack. The indictment identifies them as members of the People’s Liberation Army’s 54th Research Institute, part of China’s military. There are nine charges against them, including wire fraud, conspiracy to commit computer fraud, and economic espionage. On 13th February 2020 the Chinese Ministry of Defense released a statement about the allegations against its members, strongly denying any involvement in the hacking of Equifax.
Get hands on with the tools and techniques outlined above
Learn the techniques that Chinese nationals allegedly used to breach Equifax and expose millions of people’s data by signing up to Immersive Labs Lite. Navigate to the China vs Equifax objective, featuring red and blue team labs on jQuery-File-Uploader, SQL, and more.
Sources
https://www.techradar.com/uk/news/us-accuses-chinese-military-officers-of-equifax-hack
https://www.csoonline.com/article/3444488/equifax-data-breach-faq-what-happened-who-was-affected-what-was-the-impact.html
https://www.justice.gov/opa/press-release/file/1246891/download
https://www.businessinsider.com/doj-china-pla-military-hackers-indicted-equifax-2017-breach-2020-2?r=US&IR=T
https://www.cnet.com/news/equifaxs-hack-one-year-later-a-look-back-at-how-it-happened-and-whats-changed/