Immersive Labs Announces New Series for Incident Responders and Threat Hunters
What are they?
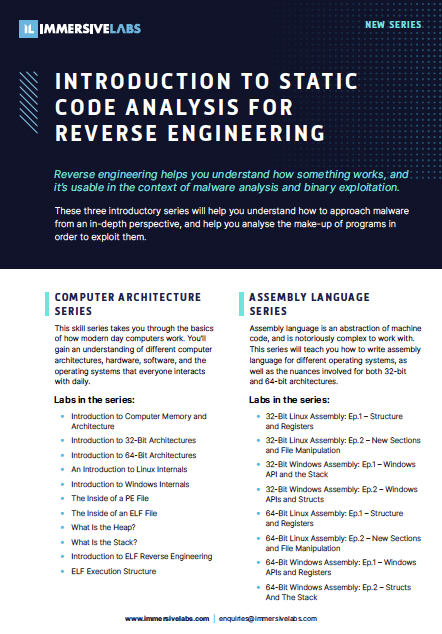
Reverse engineering helps you understand how something works, and it’s usable in the context of malware analysis and binary exploitation.
These three introductory series will help you understand how to approach malware from an in-depth perspective, and help you analyse the make-up of programs in order to exploit them.
THE SERIES:
Computer Architecture
This skill series takes you through the basics of how modern day computers work. You’ll gain an understanding of different computer architectures, hardware, software, and the operating systems that everyone interacts with daily.
Assembly Language
Assembly language is an abstraction of machine code, and is notoriously complex to work with. This series will teach you how to write assembly language for different operating systems, as well as the nuances involved for both 32-bit and 64-bit architectures.
Introduction to Reverse Engineering
Reverse engineering is one of the hardest but ultimately rewarding skills in cyber security. By completing this series of labs, you will gain hands-on reverse engineering experience, learn how the process works and understand how to begin reverse engineering an artefact.
Why are these series important?
Malware and exploits are big business – they’re exactly what companies must defend against. The series will introduce you to these practices and provide fundamental knowledge around them.
Who are they for?
- Incident Responders
- Threat Hunters
- Defense Analysts
Access to our platform is required to utilize this series. Request a demo to learn more.